$470M ‘Traffic Ticket’ Scam Hits 14 States—Americans Keep Falling For It
A fast-growing text scam has drained about $470 million from Americans in recent years, spreading across at least 14 states with fake traffic ticket alerts that demand immediate payment. Millions have received messages threatening license suspension, prosecution, or credit damage if they fail to act. The scam works because it feels routine, urgent, and official at the same time. Most victims never suspect the real goal is identity theft, not a $6.99 fee. Behind the alerts sits a system built on cheap tools and massive scale, raising a deeper question about how such a simple operation reaches so many people.
The $500 Engine Driving Millions

The entire scam runs on a budget that barely registers. Criminals buy bulk phone numbers, often sourced from breached databases, then rent SMS gateways for about $0.005 per message. Sending 100,000 texts costs roughly $500. Security researchers document campaigns pushing hundreds of thousands of messages daily. Even if only a tiny fraction respond, the returns multiply quickly. Failure costs almost nothing. Success can generate large fraud losses, recovery expenses, and stolen credentials. That tiny investment leads directly into a carefully designed payment trap.
Why $6.99 Feels So Real
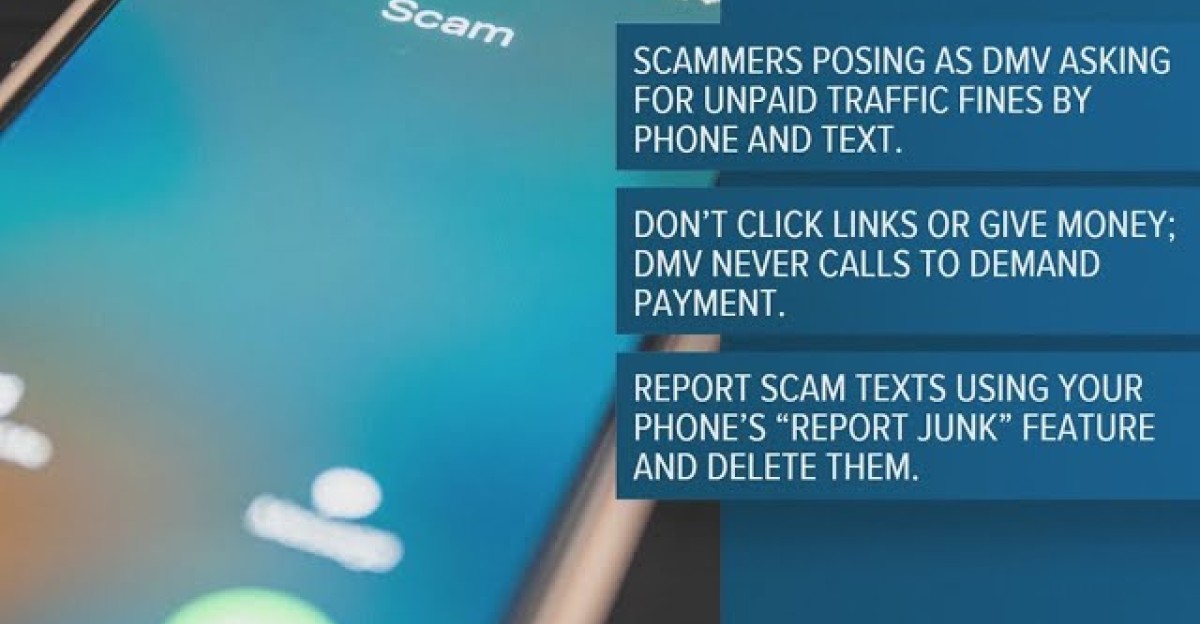
The scam text usually demands $6.99 for an “unpaid traffic violation.” That number is chosen with precision. It feels small enough to dismiss as routine, yet urgent enough to trigger quick action. Victims click a link or scan a QR code and land on a page mimicking a state DMV. They enter personal details and full credit card information. The $6.99 charge is only the opening move. The real objective is identity theft, which unfolds quietly after that first seemingly harmless payment.
What Happens After You Pay
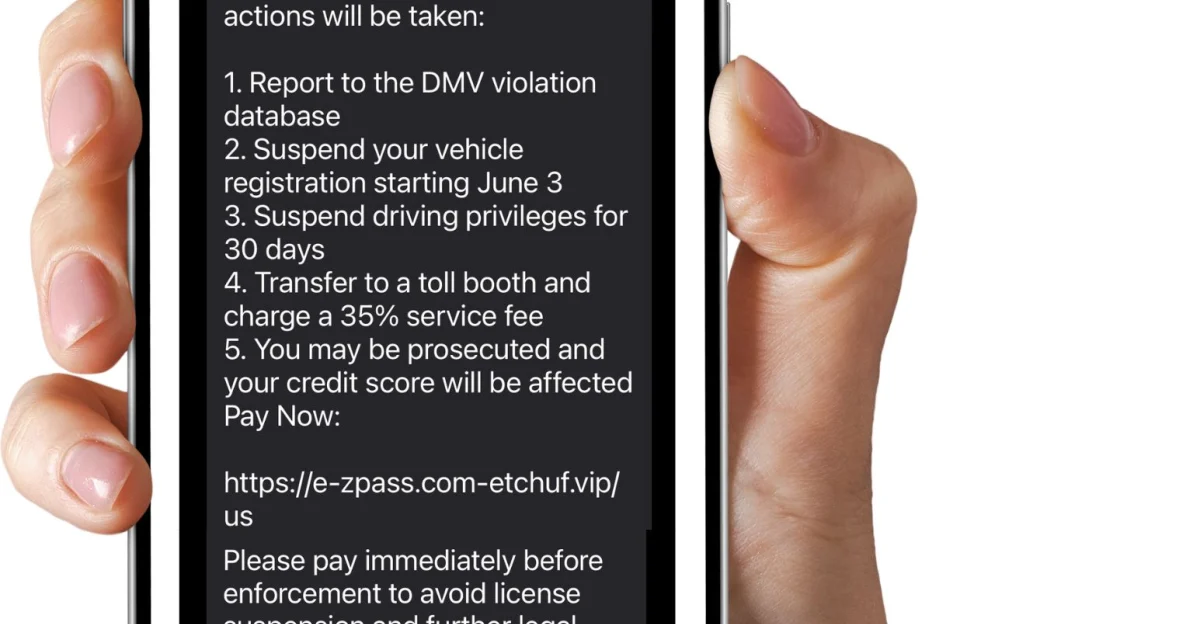
Once personal and financial data is submitted, the damage begins within days. Fraudulent transactions may appear across accounts, and stolen credentials often circulate through criminal networks for further attacks. Victims face time-consuming recovery steps such as disputing charges, freezing credit, and monitoring accounts. The initial $6.99 becomes the least costly part of the experience. This delayed impact keeps many victims unaware until the consequences escalate, raising a pressing question about how authorities are responding to such widespread deception.
States Struggle To Keep Up

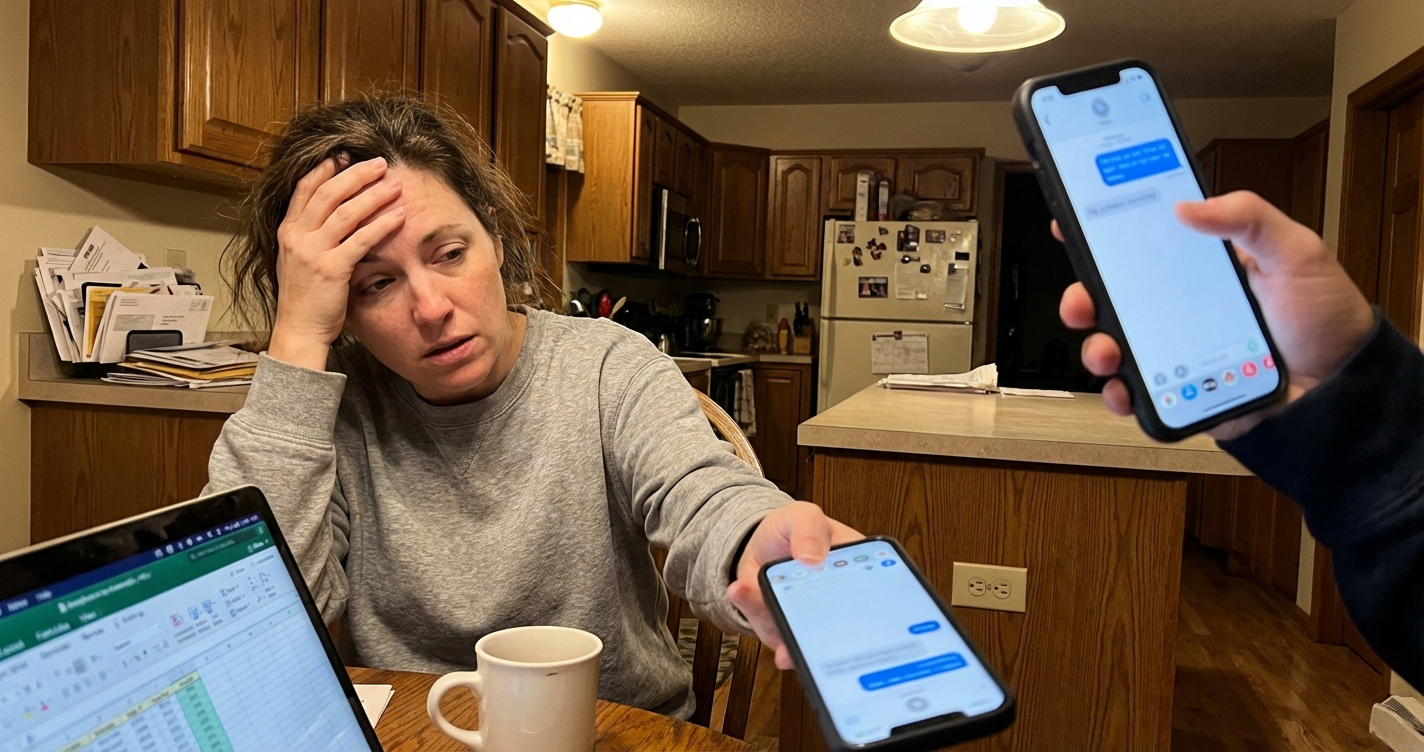
Government agencies across multiple states are now responding to waves of confusion and panic. Washington’s Department of Licensing reported residents calling about fake tickets, even though the state does not operate a DMV. Officials in Oklahoma, Michigan, and New York issued public warnings as complaints surged. WSDOT confirmed it never sends traffic ticket texts. Agencies are forced to redirect resources toward public education and damage control, creating an unexpected burden that stretches beyond financial loss and into operational strain.
QR Codes Quietly Changed The Game

The latest version of the scam replaces clickable links with QR codes embedded in messages or fake notices. Many people scan QR codes without verifying the destination, a habit shaped by everyday use in restaurants and payments. These codes redirect victims to convincing phishing sites using deceptive URLs that resemble official domains. The method feels familiar, which lowers suspicion. The shift shows how quickly tactics evolve, especially when trust in common digital tools becomes part of the attack itself.
The Infrastructure Nobody Questions

Behind every message sits a system built on legitimate tools. Bulk SMS platforms, domain registrars, and QR code generators all serve normal business needs. Yet the same systems enable large-scale fraud with little oversight. Misspelled government domains can be registered without identity checks. CAPTCHA tools, meant to block bots, now protect scam pages from detection. The overlap between legal infrastructure and criminal use creates a gap where accountability remains unclear, allowing campaigns to scale without meaningful resistance.
“That Should Be A Glaring Red Flag”

New York DMV Commissioner Mark J.F. Schroeder issued a direct warning: “You should know that DMV will never send a text like this, threatening you to make payments within days or risk suspension. That should be a glaring red flag that the message you are receiving is not actually coming from us.” The message highlights a strange reality. The tone used by scammers mimics authority so closely that official denials can sound less convincing than the fraud itself.
A Scam Model That Keeps Evolving

Law enforcement and fraud researchers have documented a clear pattern. Scams launch, warnings follow, and tactics shift. Text links gave way to QR codes, and QR codes now include CAPTCHA barriers. The strategy relies on authority, urgency, and fear to override careful thinking. Impersonating unclear or unfamiliar agencies increases confusion during moments of panic. Each adjustment arrives faster than enforcement responses, suggesting a cycle that favors adaptation and keeps victims one step behind the threat.
The Only Way To Break The Chain

Financial systems, telecom networks, and data markets all benefit indirectly from the infrastructure enabling these scams. Victims absorb the losses and the effort required to recover. The FTC notes many fraud cases go unreported, meaning $470 million likely underestimates the real impact. No legitimate government agency sends payment demands through text messages. Verifying through official .gov websites remains the safest approach. Awareness becomes the only reliable defense as this low-cost, high-volume scam continues targeting millions across the country.
Sources:
Consumer Sentinel Network Data Book 2024. Federal Trade Commission, February 2025
Text Message Scams Are on the Rise. Federal Trade Commission Consumer Alert, July 2025
DMV Warns of Text Message Scam. New York State Department of Motor Vehicles, 2025
Attorney General Warns of Fake Traffic Ticket Text Scam. Michigan Department of Attorney General, March 2026
Washington Department of Licensing Scam Alert. WA DOL, 2025
“Quishing” Attacks and QR Code Phishing Trends. Help Net Security, January 2026
Scammers Use SMS Phishing Campaigns Impersonating Government Agencies. BleepingComputer, 2025